Aadhaar (Benefits and Challenges)
Cyber-security issues related to Aadhaar have been recently noticed in Tamil Nadu impacting citizen’s data. It is not the first time that data leakage from Aadhaar has been noticed. Aadhaar usage and data security issues related to it are part of regular news content. Similarly, news regarding Aadhaar and its linkage with various accounts for availing benefits of government schemes are often reported. On one hand, Aadhaar has brought about maximum transparency and good governance at various levels whereas, on the other hand, data security issues and inaccessibility to such government recognized identity cards have been acting as a hurdle to citizens in various ways. Therefore, it has become a well-established fact that Aadhaar is acting as a boon and as well as a bane to Indians in several ways impacting their service accessibility and personal data usage.
This topic of “Aadhaar (Benefits and Challenges)” is important from the perspective of the UPSC IAS Examination, which falls under General Studies Portion.
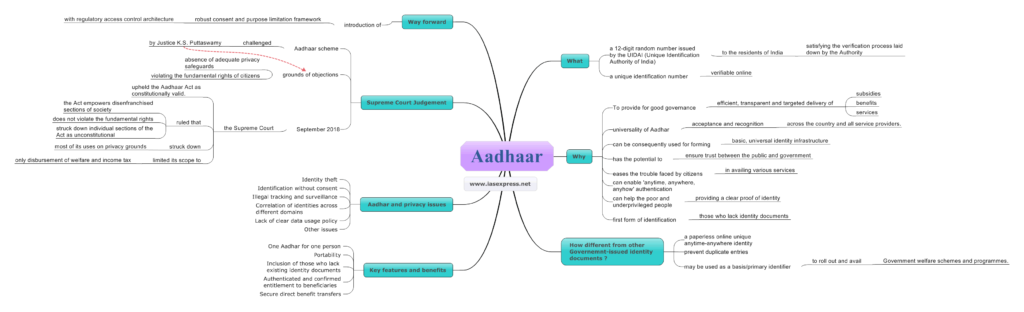
What is Aadhaar?
- Aadhaar number is a 12-digit random number issued by the UIDAI (Unique Identification Authority of India) to the residents of India after satisfying the verification process laid down by the Authority.
- The Aadhaar number is a unique identification number allotted to citizens that is verifiable online.
- Any individual, irrespective of age and gender, who is a resident of India, may voluntarily enrol to obtain an Aadhaar number.
Why Aadhaar?
- To provide for good governance, efficient, transparent and targeted delivery of subsidies, benefits and services, the expenditure for which is incurred from the Consolidated Fund of India to residents of India through assigning of unique identity numbers.
- The universality of Aadhaar ensures acceptance and recognition across the country and all service providers.
- This number can be consequently used for forming the basic, universal identity infrastructure over which registrars and agencies across the country can build their identity-based applications.
- It also has the potential to ensure trust between the public and government by eliminating the repeated KYC (Know Your Customer) checks by various government agencies for providing services.
- It also eases the trouble faced by citizens in availing various services by providing documents at different agencies every time they need them.
- The centralised technology infrastructure of the UIDAI can enable ‘anytime, anywhere, anyhow’ authentication. Aadhaar could thus give migrants mobility of identity.
- It can help the poor and underprivileged people in accessing various government and private services by providing a clear proof of identity.
- It also helps those who lack identity documents as it acts as the first form of identification they can have access to.
How is Aadhaar different from other government-issued identity documents?
- Aadhaar allows its bearer to have essentially a paperless online unique anytime-anywhere identity to cover his/her entire lifetime.
- To prevent duplicate entries, residents are enrolled into the database with proper verification of their demographic and biometric information. This ensures that the data collected is clean from the beginning of the program.
- It has the potential to eliminate duplicates and fake identities and may be used as a basis/primary identifier to roll out and avail several Government welfare schemes and programmes.
Key features and benefits
- One Aadhaar for one person – Since it is linked to an individual’s biometrics, it is safe from duplicates and fakes and thus ensures one Aadhaar number only for one person.
- Portability – As it is a universal number, it is easy for any agency or service provider across the country to authenticate a beneficiary’s identity by availing of authentication services from the central Unique Identification database.
- Inclusion of those who lack existing identity documents – Those people who lack existing identity documents are most often unable to avail various benefits which they might have been able to. Since the introduction of the Aadhaar number, many citizens are now able to avail various benefits.
- Authenticated and confirmed entitlement to beneficiaries – This service enables confirmation of the entitlement reaching the intended beneficiary.
- Secure direct benefit transfers – The UID-enabled-Bank-Account network offers a secure and low-cost platform to directly remit benefits to residents without the heavy costs associated today with benefit distribution and thus avoids leakages.
Aadhaar and privacy issues
- Identity theft – Aadhaar may be prone to practices like illegal harvesting of biometrics and identity fraud. This acts as a risk to the privacy of individuals concerned.
- Identification without consent – There are concerns regarding the unauthorized use of biometrics to identify people illegally. Elements with evil motives may identify people by inappropriate matching of fingerprint or iris scans, or facial photographs stored in the Aadhaar database, or using the demographic data.
- Illegal tracking and surveillance – Parties that are in power or private agencies and service providers may use the Aadhaar data by using the authentication and identification records and trails in the Aadhaar database for illegal and unauthorized surveillance to fulfil their vested interests.
- Correlation of identities across different domains – It may become possible to track an individual’s activities across multiple domains of service using their Aadhaar IDs, which are valid across these domains. This would lead to identification without consent.
- Lack of clear data usage policy – The lack of a clear data usage policy and regulatory framework adds to the problem. The Aadhaar users are not informed about the purpose and limitations of their data usage by third party agencies.
- Other issues – These include lack of protection against insider threats, lack of virtual identities and inadequate privacy safeguards which may hamper the civil liberties of citizens.
The Supreme Court judgement
- In 2011, the Central Government initiated a new identity document known as the Aadhaar Card.
- The Government progressively made the Aadhaar Card mandatory for numerous welfare schemes. These include subsidised food under the Public Distribution System and the Mid-Day Meal Scheme and guaranteed wage labour under the Mahatma Gandhi National Rural Employment Guarantee Scheme.
- However, the Aadhaar scheme was challenged before the Supreme Court by Justice K.S. Puttaswamy, a retired judge of the Karnataka High Court. He claimed that Aadhaar infringed upon fundamental rights guaranteed by the Constitution.
- His grounds of objections were the absence of adequate privacy safeguards on Aadhaar usage and violating the fundamental rights of citizens of availing benefits of welfare schemes provided by the governments if one does not produce his/her Aadhaar ID and limiting this right.
- On 26th September 2018, the Supreme Court upheld the Aadhaar Act as constitutionally valid.
- It ruled that the Act empowers disenfranchised sections of society by providing them better access to fundamental entitlements, such as State subsidies.
- The Court held that the Act does not violate the fundamental rights guaranteed under Articles 14, 15, 19 and 21.
- While it ruled that the Act is constitutional, it struck down individual sections of the Act as unconstitutional. It struck down most of its uses on privacy grounds and limited its scope to the only disbursement of welfare and income tax.
Way forward
Aadhaar has now evolved as one of the primary identity documents and a vital instrument for the targeted delivery of various government scheme benefits. It can hardly be negated that Aadhaar has been a major game-changer if transparency is taken into account. Yet, privacy issues remain a concern. These issues can be addressed only if a robust consent and purpose limitation framework with regulatory access control architecture is introduced. Thus, it can be concluded that Aadhaar with timely rectifications and reforms has a long way to go.
Practise Question
Q. Is it right to say that the challenges Aadhaar poses to us outweigh the benefits it provides? Comment.
- https://www.scobserver.in/court-case/constitutionality-of-aadhaar-act
- https://cacm.acm.org/magazines/2019/11/240384-privacy-concerns-with-aadhaar/fulltext
- https://uidai.gov.in/286-faqs/your-aadhaar/aadhaar-features-eligibility/1934-what-are-the-features-and-benefits-of-aadhaar.html
- https://uidai.gov.in/about-uidai/unique-identification-authority-of-india/vision-mission.html
- https://vikaspedia.in/e-governance/online-citizen-services/government-to-citizen-services-g2c/all-about-aadhaar/why-aadhaar
- https://uidai.gov.in/what-is-aadhaar.html
Awesome article 👍 good job it very helpful for the upsc begginers